Blog Ecobraz Eigre
Safe Post-Security Incident Disposal: What to Do with Compromised Devices
Introduction
Electronic devices compromised after a security incident represent significant risks to data integrity and operational continuity. The secure disposal of these devices is essential to prevent information leakage and comply with current legislation.
Identification of compromised devices
Before proceeding with disposal, it is essential to carry out a detailed inventory of all affected devices, including computers, servers, mobile devices, and storage media. This step allows mapping the risks involved and ensuring specific treatment according to the type of equipment.
Media sanitization process
To guarantee secure disposal, media sanitization is indispensable. Efficient sanitization permanently destroys stored data, making it unrecoverable and preventing unauthorized access. Recommended technologies include demagnetization, physical destruction, or encryption with elimination of cryptographic keys.
For specialized procedures, it is recommended to use certified efficient services for HD and media sanitization, ensuring full technical and legal compliance.
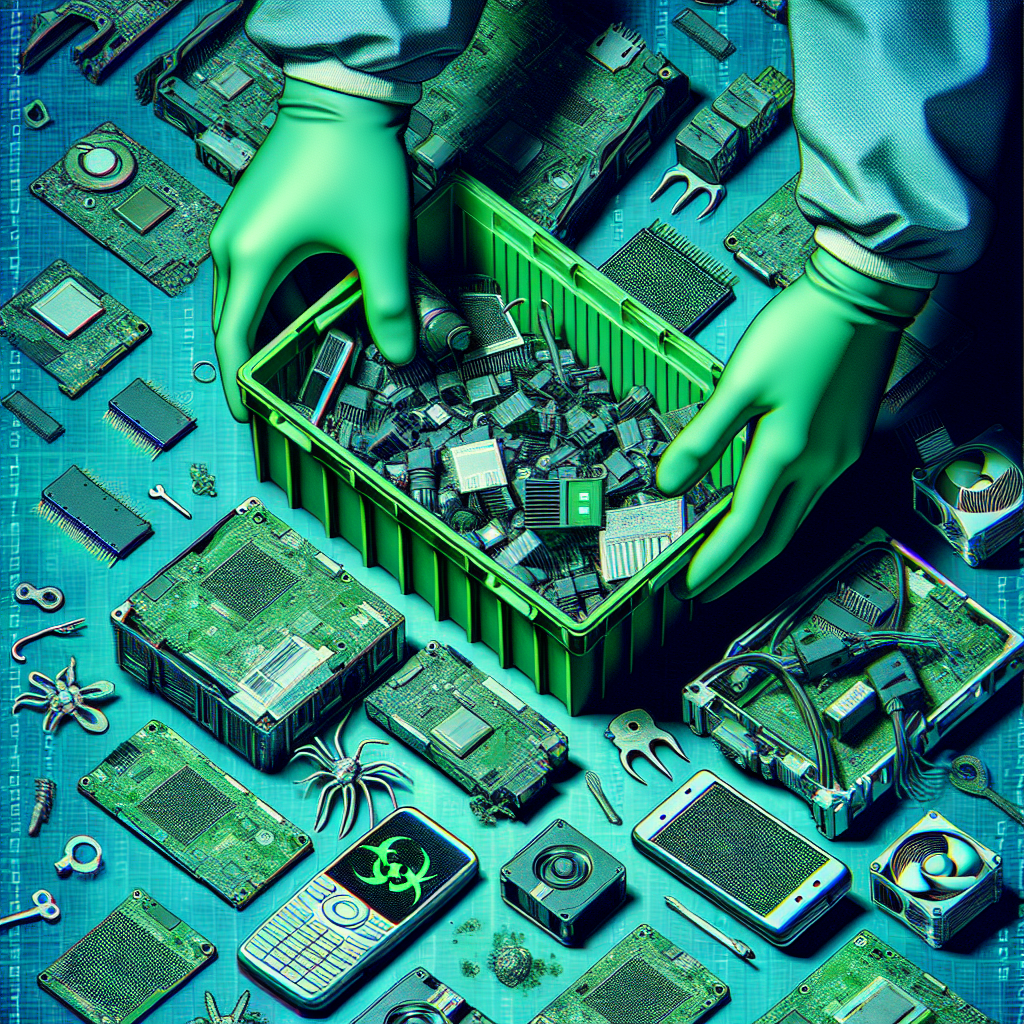
Environmentally responsible collection and disposal
After sanitization, devices must be disposed of in an environmentally correct manner, respecting electronic waste regulations. Improper disposal can cause contamination and legal penalties.
Using authorized electronic waste collection systems ensures the correct destination of components, reduces environmental impacts, and complies with the National Solid Waste Policy (Law No. 12,305/2010), regulated by Law No. 12,705/2012.
Legal and regulatory aspects
The treatment of devices post-incident must strictly observe specific legislation, such as the General Data Protection Law (Law No. 13,709/2018), which imposes accountability for proper handling of stored personal information. Additionally, NIST technical standards (NIST SP 800-88 Rev.1) provide guidance on efficient methods for media destruction and sanitization.
Documentation and audit
To ensure transparency and security, all process stages — from identification, temporary storage, sanitization to final disposal — must be properly documented and audited. This procedure assists in meeting regulatory requirements and potential forensic investigations.
Conclusion
The secure disposal of compromised devices after security incidents is essential to protect sensitive data, avoid legal risks, and minimize environmental impact. The adoption of robust technical processes and compliance with current laws and regulations are mandatory for effective and secure management of electronic assets.

Deixe um comentário
O seu endereço de e-mail não será publicado. Campos obrigatórios são marcados com *